3D printing is a $4 billion a year business, set to more than quadruple by 2020. With reports in this very blog of manufacturers already 3D printing everything from cars to bridges, art to food, office blocks to Martian villages, and calling into question the validity of many centuries-old production practices, it really does feel like stepping into the future. Similar, in fact, to the emergence of the silicon age, back in the seventies.
Indeed, the FAA recently certified the first 3D-printed part for a commercial jet engine and, with companies like Ford using additive manufacturing to build parts and prototypes, we are already entrusting our lives to 3D-printed equipment on an almost daily basis.
However, in also similar to the electronics and computing industries, this new technology is beginning to be threatened by some of the same dangers as trusted, only partially trusted, and sometimes untrusted parties are becoming part of the global supply chain.
A team of cybersecurity and materials engineers at the NYU Tandon School of Engineering has published a paper in The journal of the Minerals, Metals & Materials Society, in which they reveal their findings and, thankfully, offer some initial recommendations to combat the issue.

The team, which included Steven Eric Zeltmann, a graduate student in mechanical engineering, Nikhil Gupta, noted materials researcher and an associate professor at the Tandon School of Engineering, and Ramesh Karri, professor of electrical and computer engineering, examined two aspects of 3D printing that have cyber security implications: printing orientation and insertion of fine defects
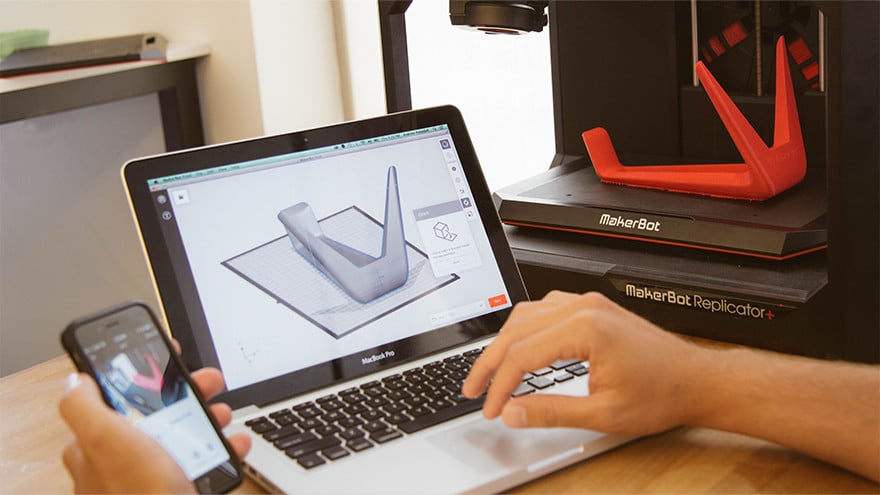
3D printers, as you’re all no doubt aware, build from a CAD file sent to it by a designer. Manufacturing software then analyses the design, breaks it down into slices and positions the printer head so the printer can apply the materials in ultra-thin layers.
‘These are possible foci for attacks that could have devastating impact on users of the end product, and economic impact in the form of recalls and lawsuits,’ said Gupta, speaking of how the CAD files received by printing companies do not give instructions for printer head positioning. As the orientation of the head or the product during printing could cause as much as a 25% variation in its inherent strength, this means anyone wishing to cause issues with the end product could do so almost without detection. ‘With 3D printed components,’ he continued, ‘such as metallic moulds made for injection moulding used in high temperature and pressure conditions, such defects may eventually cause failure.’
The researchers found that when they introduced sub-millimetre defects between printed layers, the defects were undetectable by common industrial monitoring techniques like ultrasonic imaging and, over time, the materials would weaken due to fatigue, heat, light, and humidity, becoming more vulnerable to these small defects.
Ramesh Karri, known for his work on improving the reliability of the global microchip supply chain, said, ‘With the growth of cloud-based and decentralized production environments, it is critical that all entities within the additive manufacturing supply chain be aware of the unique challenges presented to avoid significant risk to the reliability of the product.’
His most chilling point is how simple it can be for an attacker to hack into any 3D printer that’s connected to the internet and introduce internal defects at the printing stage that no one would discover until the part failed.
Zeltmann, the paper’s lead author, suggested that to guard against these cyber risks, companies should not keep their 3D printers connected to the internet to avoid them being compromised by remote attacks.
He also suggested that manufacturers should do more to encrypt their design files, ensuring only their printers can read and use them. These steps should protect the manufacturers’ intellectual property – the design files – as well as the integrity of their printed components.
